(a) i() What is firewall? (ii) List two methods used in protecting the computer system. (b) Explain the following stages of the System Development Life Cycl...
Question 1 Report
(a) i() What is firewall? (ii) List two methods used in protecting the computer system.
(b) Explain the following stages of the System Development Life Cycle: (i) feasibility study; (ii) design; (iii) maintenance.
Download The App On Google Playstore
Everything you need to excel in JAMB, WAEC & NECO
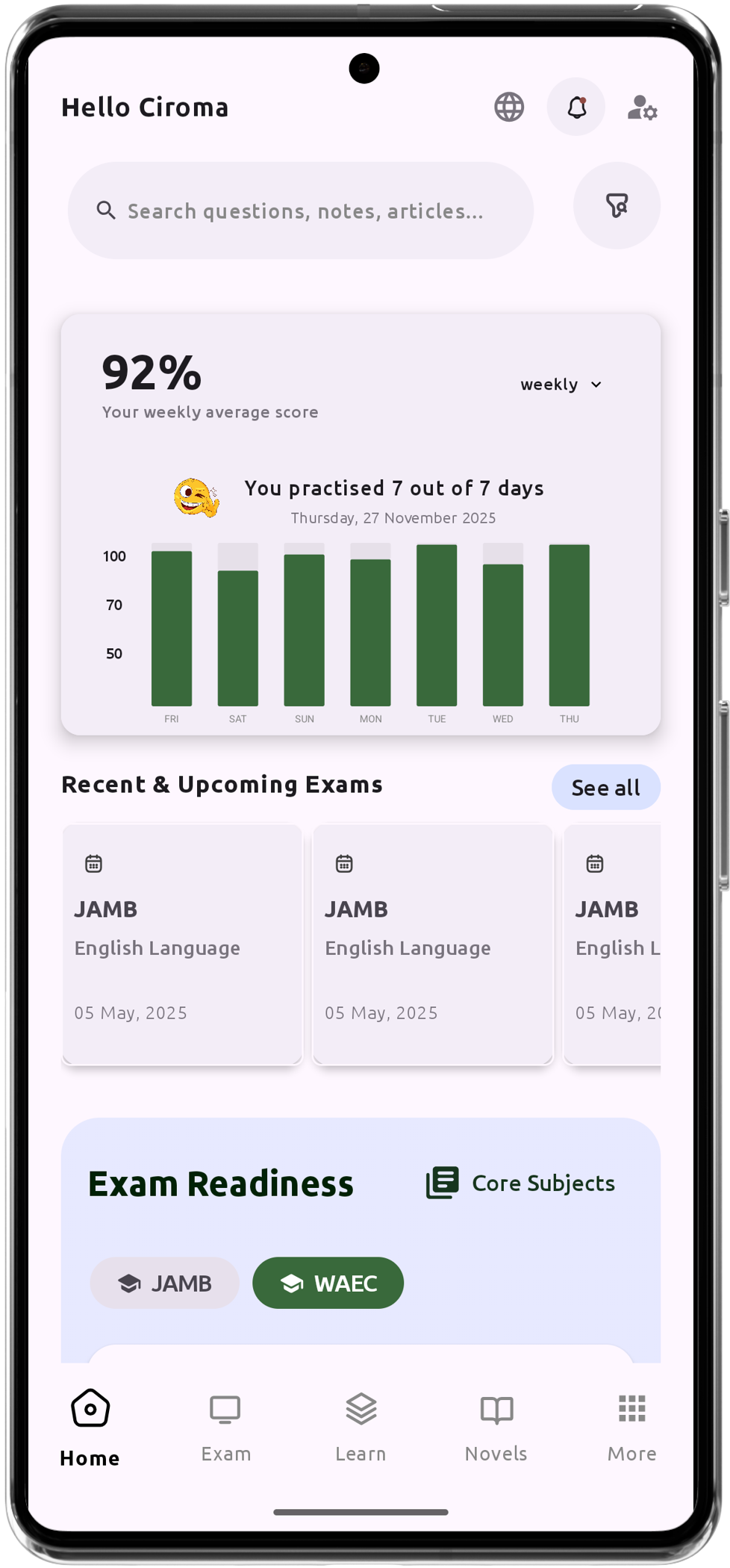
Personalized AI Learning Chat Assistant
Thousands of JAMB, WAEC & NECO Past Questions
Over 1200 Lesson Notes
Offline Support - Learn Anytime, Anywhere
Green Bridge Timetable
Literature Summaries & Potential Questions
Track Your Performance & Progress
In-depth Explanations for Comprehensive Learning