(a)(i) Define the term encryption. (ii) Tick two authentication techniques involved in security measure from Table 1. Table 1 (ii) Outline two features of d...
Question 1 Report
(a)(i) Define the term encryption. (ii) Tick two authentication techniques involved in security measure from Table 1.
Table 1
(ii) Outline two features of data encryption. (b) While exchanging data with a friend through your mobile phone, you observed that it took a longer time than usual. Outline four factors that may be responsible for the delay in the data transfer.
| TECHNIQUE |
TICK() |
| Firewall |
|
| Biometric |
|
| Password |
|
| Intranet |
Download The App On Google Playstore
Everything you need to excel in JAMB, WAEC & NECO
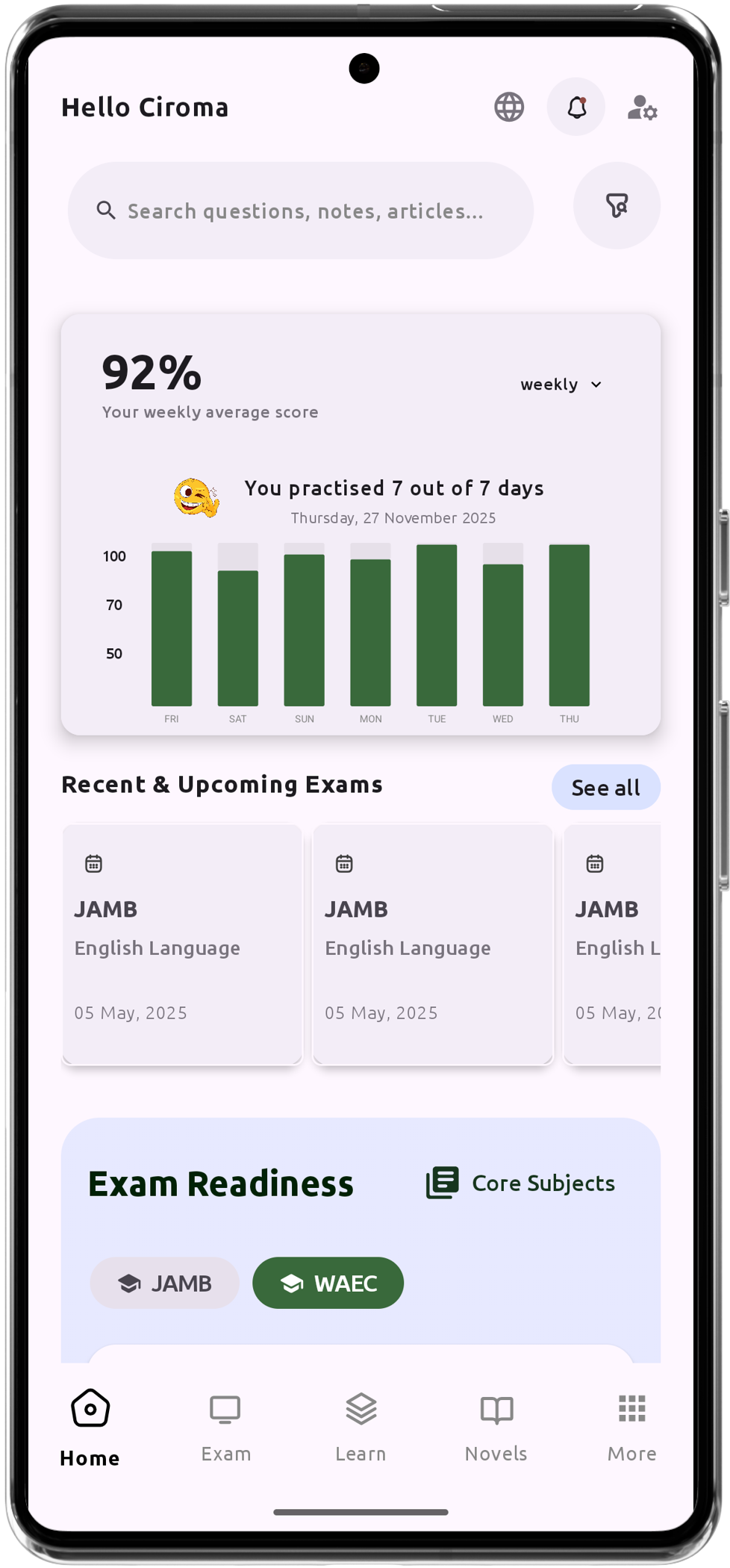
Personalized AI Learning Chat Assistant
Thousands of JAMB, WAEC & NECO Past Questions
Over 1200 Lesson Notes
Offline Support - Learn Anytime, Anywhere
Green Bridge Timetable
Literature Summaries & Potential Questions
Track Your Performance & Progress
In-depth Explanations for Comprehensive Learning